A critical zero-day vulnerability in BigAntSoft’s BigAnt Server (CVE-2025-0364) allows unauthenticated attackers to execute arbitrary code on affected systems through a chain of SaaS registration abuses and PHP file uploads.
The flaw, discovered by VulnCheck researchers during an analysis of a misrated CVSS score for CVE-2024-54761, impacts all versions ≤5.6.06 of the Windows-based enterprise chat platform.
The exploit chain begins with a default-enabled SaaS registration portal at /index.php/Home/Saas/reg_email.html, which permits organizational account creation after solving a basic CAPTCHA challenge.
BigAnt Server 0-Day Vulnerability
Attackers leverage this to create administrative accounts tied to attacker-controlled SaaS organizations.
The registration process exposes critical session variables through debug endpoints like /index.php/Addin/login/index.html, enabling UUID extraction for SaaS activation.
Post-registration, attackers manipulate session cookies to hijack the SaaS context. This forces the server to bind the session to the malicious SaaS organization, allowing access to the Cloud Drive Add-in.
The system improperly validates file uploads in the Add-in module, accepting PHP files without authentication checks.
VulnCheck’s published exploit automates the 10-step attack sequence:
- CAPTCHA harvesting via /index.php/Home/Public/verify
- SaaS organization registration with administrative privileges
- Session fixation through cookie manipulation
- UUID leakage via debug endpoints
- SaaS activation through crafted saas_id parameter
- Authentication to Cloud Drive using default admin credentials
- PHP payload upload to /index.php/addin/public/load/clientid/1.html
- Unauthenticated trigger of uploaded shell at /data/{UUID}/pan/{PATH}/malicious.php
The exploit grants NT AUTHORITYSYSTEM privileges.
The vulnerability arises from multiple architectural flaws:
Insecure Defaults: The SaaS registration portal remains active without installation hardening, using predictable credentials (admin/registration password) for Cloud Drive access.
Session Management Failures: The sp_saas_id() function in site.php exposes UUIDs through unauthenticated API demo pages, allowing SaaS context hijacking.
Unrestricted File Uploads: The Cloud Drive module (Application/Addin/Controller/CloudController.class.php) lacks file type validation, permitting direct PHP execution under C:Program Files (x86)BigAntSoftIM Consoleim_webserverhtdocsdata
Mitigations
BigAntSoft has not issued an official patch as of March 2025. Organizations should:
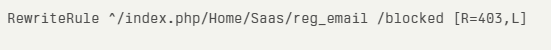
- Disable SaaS registration via Apache/Nginx rewrite rules:
- Implement WAF rules to block PHP uploads to /data/*/pan/ paths
- Audit sys_saas table entries for unauthorized organizations
- Monitor process creation for php-cgi.exe spawning cmd.exe
Researchers notes this highlights systemic CVSS scoring inaccuracies, as the original CVE-2024-54761 required administrative access while this 0-day operates without authentication.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.

